hermes hacked | hermes hac 40 price hermes hacked When Hermes is executed, it will also use a User Account Control, or UAC, bypass called Eleven, or Elevation by environment variable expansion, to delete a victim's Shadow Volume . See more Single Cask & 1st Fill Sherry Butt. Aberlour 16 Year Old 2022 Distillery Reserve .
0 · original birkin bags by hermes
1 · most expensive hermes bag ever
2 · hermes most expensive item
3 · hermes hac price
4 · hermes hac a dos price
5 · hermes hac 50 bag
6 · hermes hac 40 price
7 · hermes birkin so black
Les meilleures activités à Malte, Europe : découvrez 1 046 746 avis de voyageurs et photos de 2 086 choses à faire à Malte, sur Tripadvisor.
While analyzing the Hermes sample, Fabian found that the seed used to generate the encryption key could be attacked in order to create a decryptor. Once this was . See more
As described in the previous section, Hermes will use a UAC bypass to execute a batch file called shade.bat. This batch file, shown below, will not only delete the computer's shadow volumes, but will also delete backup images that may be present on the computer. It . See moreWhen Hermes is executed, it will also use a User Account Control, or UAC, bypass called Eleven, or Elevation by environment variable expansion, to delete a victim's Shadow Volume . See moreWhen the Hermes Ransomware is executed, it will copy itself to C:\Users\Public\Reload.exe and execute itself. It will then . See more
North Korean hackers used Hermes ransomware to hide their fraudulent transactions and encrypt bank data after stealing million from FEIB in Taiwan. Hermes ransomware is a modified .
WASHINGTON: The U.S. Government is investigating the unauthorized access to commercial telecommunications infrastructure by actors affiliated with the People’s Republic of . Like all ransomware, Hermes locks a victim’s files and demands payment to unlock them. Emsisoft battles ransomware like this on the front line daily, with the creation of free . Hermes is a ransomware-type malware that encrypts files using RSA-2048 cryptography and demands ransom for decryption. Learn how to remove it, restore your files, .

Learn how to turn your Ikea Hemnes furniture into something that looks expensive and stylish with these 14 hacks. From dresser to daybed, from kitchen pantry to shoe storage, . Hermit spyware is a sophisticated malware attack that can infect iOS and Android devices using zero-day vulnerabilities and exploits. Learn how it works, who is behind it, and .
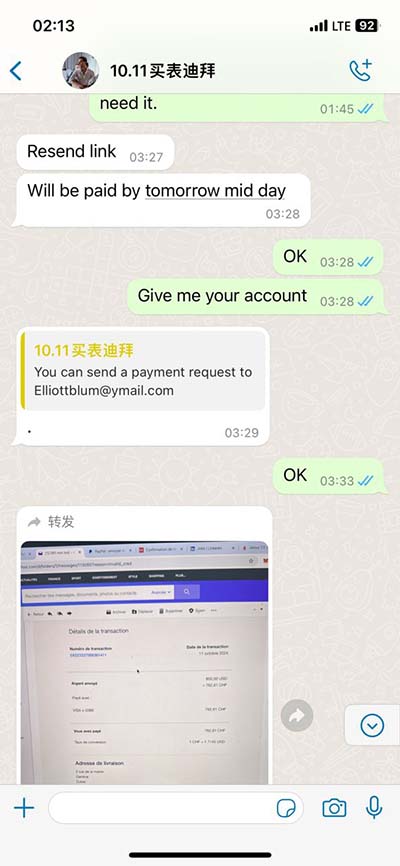
August 20, 2018. 01:01 PM. A malspam campaign is underway that pretends to be an invoice for an outstanding payment. When these invoices are opened they install the AZORult information .
The HAC is one of the oldest bags created by Hermès. With its own unique and particular style, it was originally designed to carry riding equipment such as saddles and boots. . "My Hermes or any other delivery company mentioned in these emails have not been hacked or had their email or other servers compromised. They are not sending the . Learn how Hermes ransomware encrypts files, deletes backups and demands ransom. Watch how Emsisoft's Fabian Wosar decrypted Hermes live and how to protect yourself with Emsisoft Anti-Malware. North Korean hackers used Hermes ransomware to hide their fraudulent transactions and encrypt bank data after stealing million from FEIB in Taiwan. Hermes ransomware is a modified version.
WASHINGTON: The U.S. Government is investigating the unauthorized access to commercial telecommunications infrastructure by actors affiliated with the People’s Republic of China.
original birkin bags by hermes
Like all ransomware, Hermes locks a victim’s files and demands payment to unlock them. Emsisoft battles ransomware like this on the front line daily, with the creation of free decrypters to help victims get their files back.
Hermes is a ransomware-type malware that encrypts files using RSA-2048 cryptography and demands ransom for decryption. Learn how to remove it, restore your files, and report it to authorities. Learn how to turn your Ikea Hemnes furniture into something that looks expensive and stylish with these 14 hacks. From dresser to daybed, from kitchen pantry to shoe storage, see how to paint, decal, trim and more. Hermit spyware is a sophisticated malware attack that can infect iOS and Android devices using zero-day vulnerabilities and exploits. Learn how it works, who is behind it, and what you can do.
August 20, 2018. 01:01 PM. A malspam campaign is underway that pretends to be an invoice for an outstanding payment. When these invoices are opened they install the AZORult information stealing.
The HAC is one of the oldest bags created by Hermès. With its own unique and particular style, it was originally designed to carry riding equipment such as saddles and boots. Emile-Maurice Hermès – the grandson of the company founder, Thierry Hermès – . "My Hermes or any other delivery company mentioned in these emails have not been hacked or had their email or other servers compromised. They are not sending the emails to you. Learn how Hermes ransomware encrypts files, deletes backups and demands ransom. Watch how Emsisoft's Fabian Wosar decrypted Hermes live and how to protect yourself with Emsisoft Anti-Malware. North Korean hackers used Hermes ransomware to hide their fraudulent transactions and encrypt bank data after stealing million from FEIB in Taiwan. Hermes ransomware is a modified version.
WASHINGTON: The U.S. Government is investigating the unauthorized access to commercial telecommunications infrastructure by actors affiliated with the People’s Republic of China. Like all ransomware, Hermes locks a victim’s files and demands payment to unlock them. Emsisoft battles ransomware like this on the front line daily, with the creation of free decrypters to help victims get their files back. Hermes is a ransomware-type malware that encrypts files using RSA-2048 cryptography and demands ransom for decryption. Learn how to remove it, restore your files, and report it to authorities.
Learn how to turn your Ikea Hemnes furniture into something that looks expensive and stylish with these 14 hacks. From dresser to daybed, from kitchen pantry to shoe storage, see how to paint, decal, trim and more. Hermit spyware is a sophisticated malware attack that can infect iOS and Android devices using zero-day vulnerabilities and exploits. Learn how it works, who is behind it, and what you can do.August 20, 2018. 01:01 PM. A malspam campaign is underway that pretends to be an invoice for an outstanding payment. When these invoices are opened they install the AZORult information stealing. The HAC is one of the oldest bags created by Hermès. With its own unique and particular style, it was originally designed to carry riding equipment such as saddles and boots. Emile-Maurice Hermès – the grandson of the company founder, Thierry Hermès – .
most expensive hermes bag ever
ABHISHEK OVERSEAS currently has strategic partners in major Sea & Air ports across the world. We are specialize in handling Door to Door shipments, courier.
hermes hacked|hermes hac 40 price